Understanding X-Content-Type-Options
The X-Content-Type-Options is an HTTP response header that plays a critical role in web security. Its primary purpose is to mitigate certain types of security risks associated with content types in HTTP responses.
How X-Content-Type-Options Works
The X-Content-Type-Options header is straightforward in its operation. When a web server sends a response to a browser, it can include this header with one of two values:
- nosniff: This value instructs the browser not to “sniff” or guess the content type of the response. Instead, it must trust the content type provided by the server. If the server declares a response as “text/html,” the browser must treat it as such, even if the content appears to be of a different type.
- none: This value effectively disables the X-Content-Type-Options header, allowing the browser to use its content type sniffing behavior. However, using “none” is generally not recommended for security reasons.
Why X-Content-Type-Options Is Essential
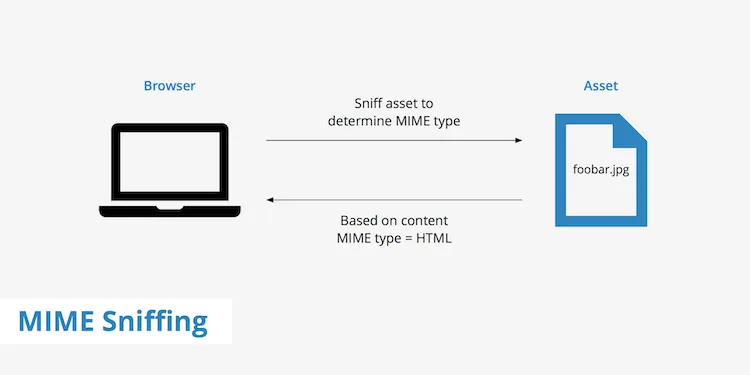
- Mitigating MIME Sniffing: One of the main purposes of X-Content-Type-Options is to prevent MIME (Multipurpose Internet Mail Extensions) sniffing, where browsers attempt to interpret the content type of a response based on its content. This can lead to security vulnerabilities when attackers manipulate response content to exploit MIME sniffing.
- Preventing Content Type Attacks: Attackers may attempt to disguise malicious content as benign by manipulating the response content type. X-Content-Type-Options helps ensure that browsers always interpret content types correctly, reducing the risk of content-based attacks.
- Compatibility with Other Security Measures: X-Content-Type-Options works harmoniously with other security headers, such as Content-Security-Policy (CSP) and Cross-Origin Resource Sharing (CORS), to create a comprehensive web security strategy.
- Enhancing User Trust: When users visit your website, they want assurance that the content they’re interacting with is legitimate and secure. Implementing security headers like X-Content-Type-Options helps maintain user trust by preventing potential content-based attacks.
Implementing X-Content-Type-Options
Implementing the X-Content-Type-Options header is relatively simple. Web developers can configure their web servers to include this header in the HTTP response sent to the client’s browser. The header should typically be set to “nosniff” to ensure the browser does not perform content type sniffing.
For Apache servers, you can add the header to your configuration using the “Header” directive. In Nginx, you can use the “add_header” directive within the server block.
Conclusion
The X-Content-Type-Options header is a valuable security tool that should not be overlooked when designing and securing your website. By preventing MIME sniffing and content-based attacks, it contributes to a more robust defense against potential vulnerabilities. As part of a comprehensive security strategy, X-Content-Type-Options helps protect your website and its users, ensuring a safer and more trustworthy online experience.