In the intricate realm of cyber threats, an insidious adversary known as “clickjacking” lurks, employing cunning techniques to manipulate user interactions for nefarious gains. This sophisticated attack method capitalizes on user trust and the invisibility of certain web elements, posing a significant risk to the security and privacy of unsuspecting individuals. This article unveils the mechanics of clickjacking, delves into its far-reaching consequences, and offers insights into real-world scenarios where this invisible menace wreaks havoc.
The Art of Deception: Clickjacking Unveiled
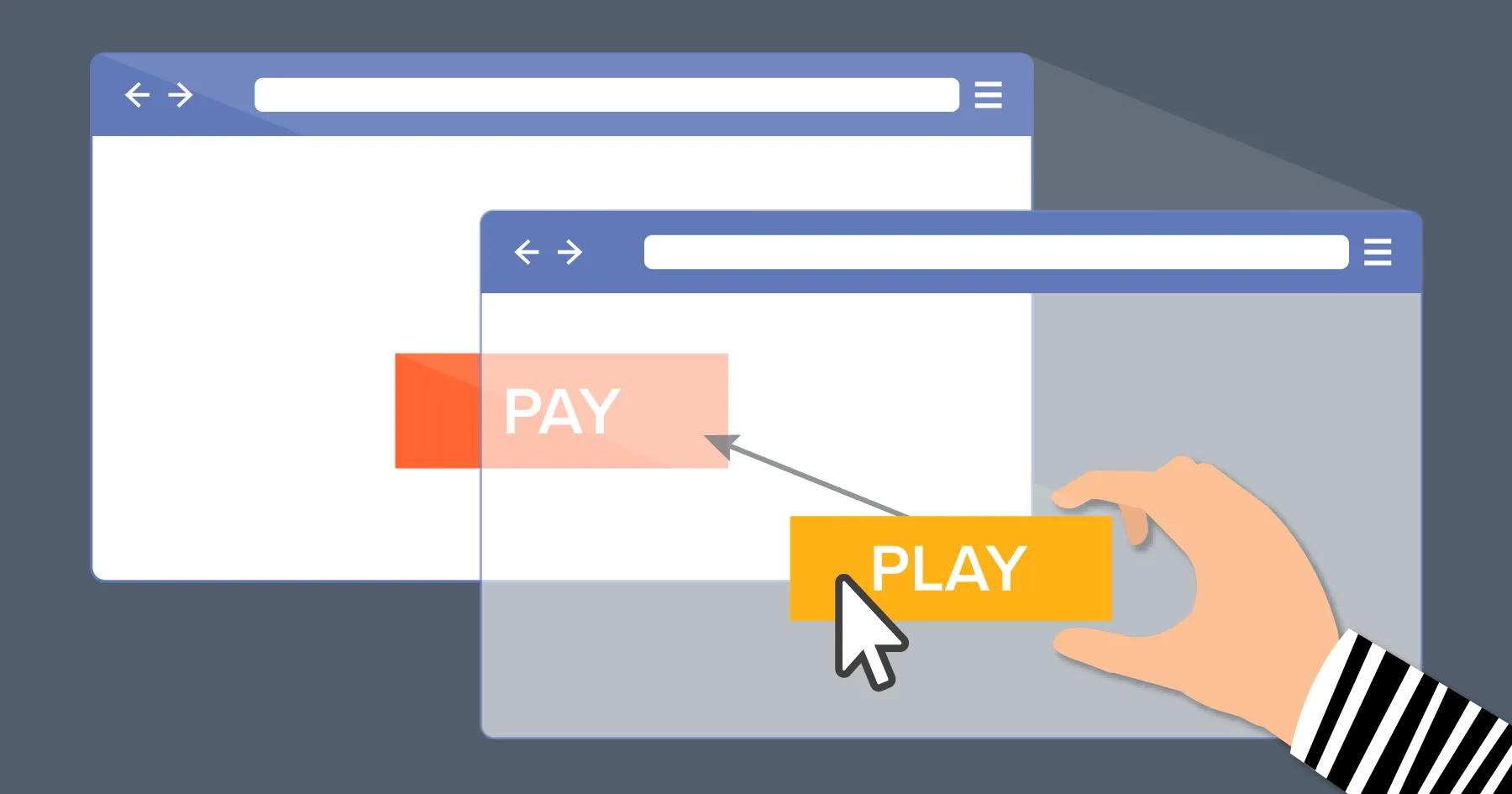
Clickjacking represents a cunning assault on user interactions within web interfaces. This nefarious technique ensnares users by presenting them with seemingly legitimate web elements that conceal an ulterior purpose. In reality, these masked elements harbor malicious intent, directing users to perform actions they neither intended nor consented to. The attackers achieve this by strategically overlaying invisible or misleading elements on top of genuine content.
The Complex Dance of Elements
A common manifestation of clickjacking involves embedding an invisible page or HTML element within an iframe, expertly positioned over the visible content users interact with. This manipulation plays out surreptitiously, tricking users into believing they are engaging with a genuine element while actually interacting with the concealed layer. This digital sleight of hand is executed with precision, exploiting users’ trust and visual cues to their detriment.
Beyond the Click: The Devastating Consequences
Clickjacking’s consequences extend beyond the mere act of clicking on disguised elements. By luring users into unwittingly executing actions, attackers can orchestrate a range of malicious outcomes:
- Unauthorized Transactions: Users innocently execute financial transactions or subscriptions without their awareness, draining resources.
- Covert Data Harvesting: Deceptive forms can surreptitiously collect sensitive data, such as login credentials and personal information.
- Perilous Permissions: Users may unknowingly grant permissions to access their devices, enabling remote control and potential harm.
- Malicious Downloads: Hidden clicks can trigger downloads of malware or ransomware, compromising devices and data.
- Social Engineering: Clickjacking can manipulate users into sharing confidential data on social media platforms, facilitating identity theft.
A Glimpse into a Clickjacking Scenario
Imagine encountering a captivating webpage that promises an enticing free trip to a tropical paradise. Unbeknownst to the user, behind the scenes, a malicious actor scrutinizes the user’s banking site login status. If logged in, a screen facilitating fund transfers is loaded, embedding the attacker’s bank details into the form. This malicious fund transfer page remains concealed in an invisible iframe, strategically positioned above the alluring “Receive Gift” button.
As users click the seemingly innocuous “Book My Free Trip” button, they inadvertently trigger the concealed iframe’s “Confirm Transfer” button. The result: funds are surreptitiously siphoned off to the attacker’s account, leaving users redirected to a seemingly innocuous page detailing their “free gift,” blissfully unaware of the digital heist that unfolded behind the scenes.
Protecting Against Clickjacking: Your Armor of Vigilance
Fortunately, robust defense strategies exist to shield against clickjacking:
- Stay Educated: Enhance your awareness of clickjacking techniques and evolving threats.
- Implement Security Measures: Employ web security tools and extensions designed to identify and counter clickjacking attempts.
- Verify URLs: Scrutinize URLs and cross-reference with official sources to ensure authenticity.
- Update Regularly: Keep your software, browsers, and security solutions updated to stay fortified against vulnerabilities.
- Trust but Verify: Be cautious when interacting with unfamiliar or too-good-to-be-true offers, and always verify their legitimacy.
Conclusion: Vigilance Against the Unseen
As we navigate the intricate digital landscape, clickjacking stands as a testament to the ever-evolving sophistication of cyber threats. With its ability to dupe even the most cautious users, understanding clickjacking’s mechanics is paramount to safeguarding your digital presence. By staying informed, adopting best security practices, and exercising caution in your online interactions, you can fortify your defenses against this invisible foe, ensuring that every click aligns with your intentions, not those of malicious actors.
Additional Resources: For a deeper dive into clickjacking, visit this Wikipedia link.